On April 1st (and I wish this were an April Fool's joke), a fraudulent invoice landed in our church's Accounts Payable inbox. It had a W-9. It had two professionally formatted PDF invoices. It had a fabricated email thread where our lead pastor appeared to have already approved the charges and told AP to pay.
It was the most sophisticated single-shot social engineering attack I've ever seen hit a church. I've seen larger dollar amounts. I've never seen one this self-contained: every piece of the puzzle included in a single email, ready to process without a single follow-up question. It almost got me. And for a few hours, it sat in our shared mailbox looking completely legitimate.
A Note on Scam Tolerance
I should be transparent: I am not an easy mark. I enjoy messing with scammers. I have held phone scammers on the line for the pure sport of wasting their time.
I once kept an IRS impersonator on the phone for 45 minutes while I drove down the highway, pretending to desperately try (and frustratingly fail) at following all of his instructions. Poor guy tried super hard to be patient. When I got to my destination, I told him I was sorry, it had been fun, but I had a meeting to get to, so I wouldn't be giving him any money.
He tried very hard to keep the act going. The IRS was coming after me. I'd be arrested. This was my last chance.
I told him I'd give him the money right now if he could answer one question:
“What does IRS stand for?”
He told me it stands for "F* You," and hung up.
I'm telling that story not because it's funny (it is), but because it matters for context. I am not someone who gets rattled by a phishing email. I look forward to them. And this one gave me pause. It almost got me. I could see exactly how someone without my particular brand of paranoia would have believed it completely. The fabricated thread, the W-9, the two invoices, the lead pastor's real name, the alignment with real events at our church. It was built to pass every reasonable checkpoint a normal AP workflow would throw at it.
The only thing that stopped it was a five-second question in a hallway.
What Landed in the Inbox
The email came from "Sam Zappa," display name only. The actual sending address was [email protected], a throwaway account on a Norwegian privacy-focused email provider. The body referenced [email protected] as the contact, a free email forwarding service dressed up to look like a consulting firm.
The subject line: "Fwd: Invoice 20268887 for Adam B’s VIP Membership is Due."*
Adam B* is our lead pastor. Not a made-up name. Not a guess. They researched our church and used the name of the person whose authority would carry the most weight with an AP processor.
The cover email was short, professional, and hit every pressure point an AP person would feel:
Please note that this is a monthly subscription, and the account is currently two months outstanding. As a courtesy, a $1,000 discount was applied to the first month's invoice. Given that the remaining balance remains overdue, we would greatly appreciate settlement today if possible.
Then, the instruction that completes the trap: "All future replies must cc Bradley Raley at [email protected]." A second attacker-controlled address, ready to intercept any follow-up.
Attached: three PDFs.
The Attachments
A completed W-9.
IRS Form W-9, Rev. March 2024. Name: Sam Zappa. Individual/sole proprietor. Address in Omaha, Nebraska. Social Security number filled in. Signature dated January 12, 2026.
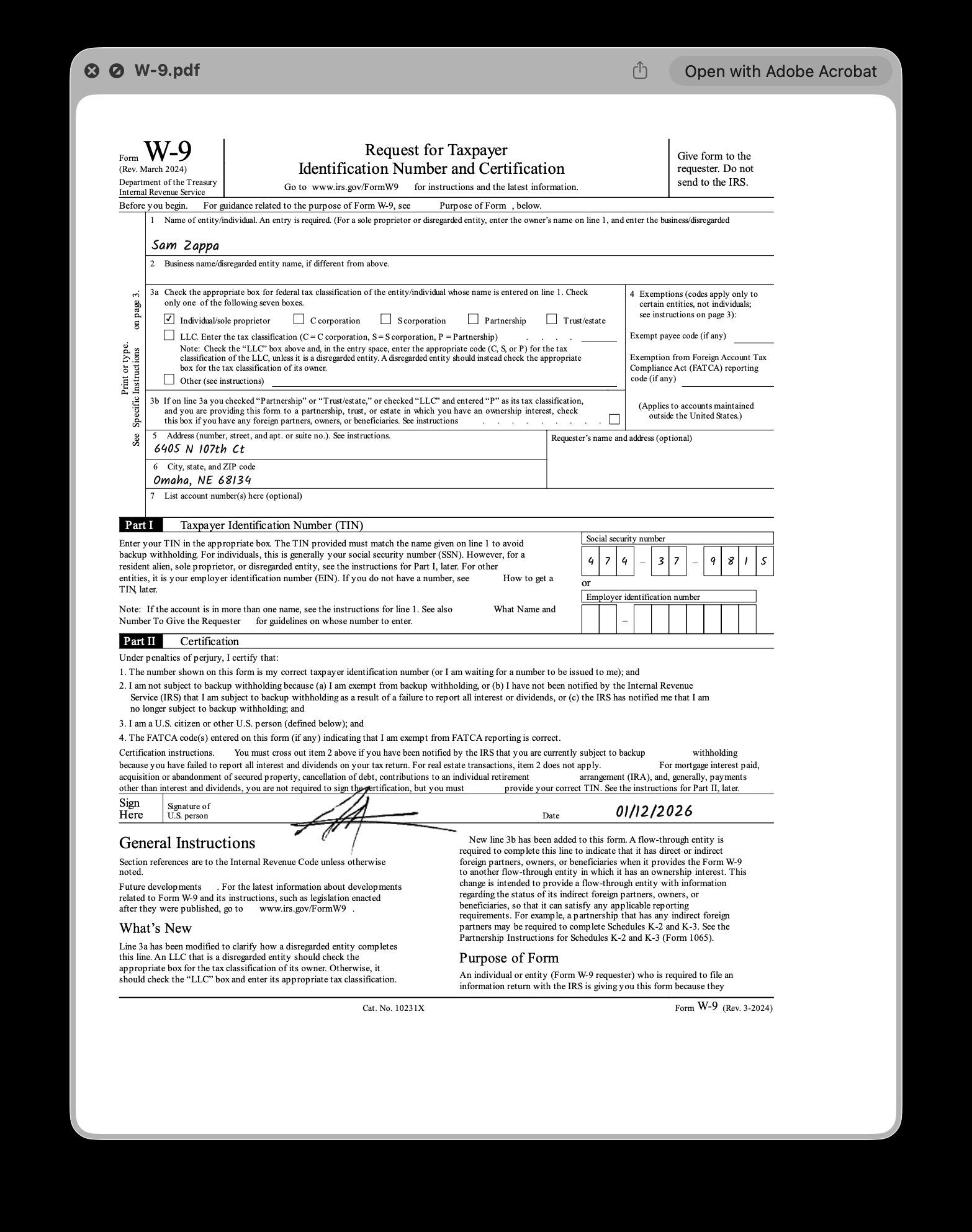
This is the detail that elevates the attack from "spam" to "social engineering." Most AP departments require a W-9 on file before issuing payment to a new vendor. That requirement is a natural firewall. It forces a back-and-forth conversation that would expose the fraud. By including a completed W-9 upfront, the attacker removed the one procedural step most likely to generate a phone call.
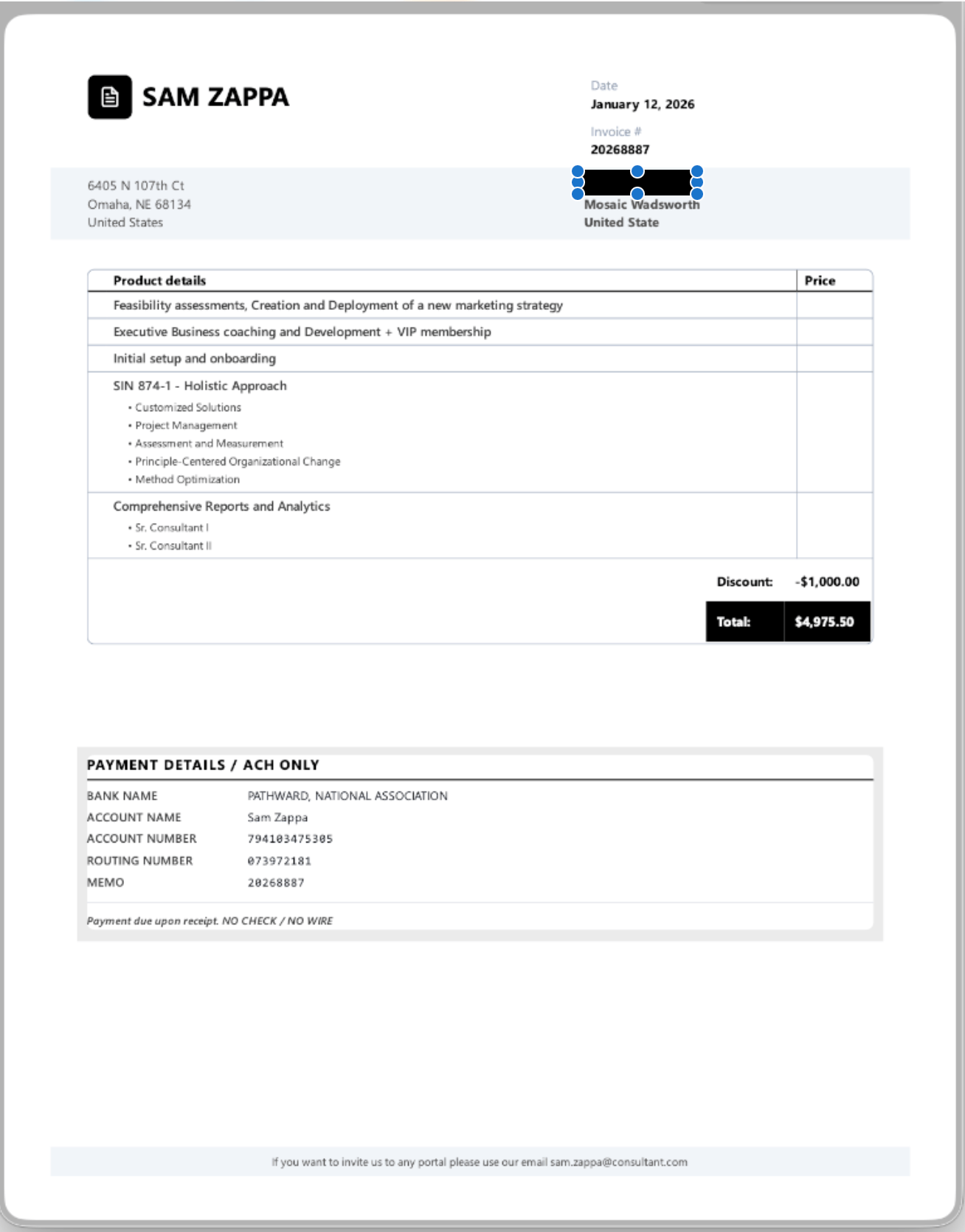
Invoice #20268887, January, $4,975.50.
Dated January 12, 2026. Line items included "Feasibility assessments, Creation and Deployment of a new marketing strategy," "Executive Business coaching and Development + VIP membership," and a reference to "SIN 874-1, Holistic Approach," an actual GSA Schedule category for consulting services. None of the line items had individual prices. The total just appeared at the bottom, with a $1,000 discount applied.
Invoice #20297570, February, $5,975.50.
Same line items. No discount this time. Full price.
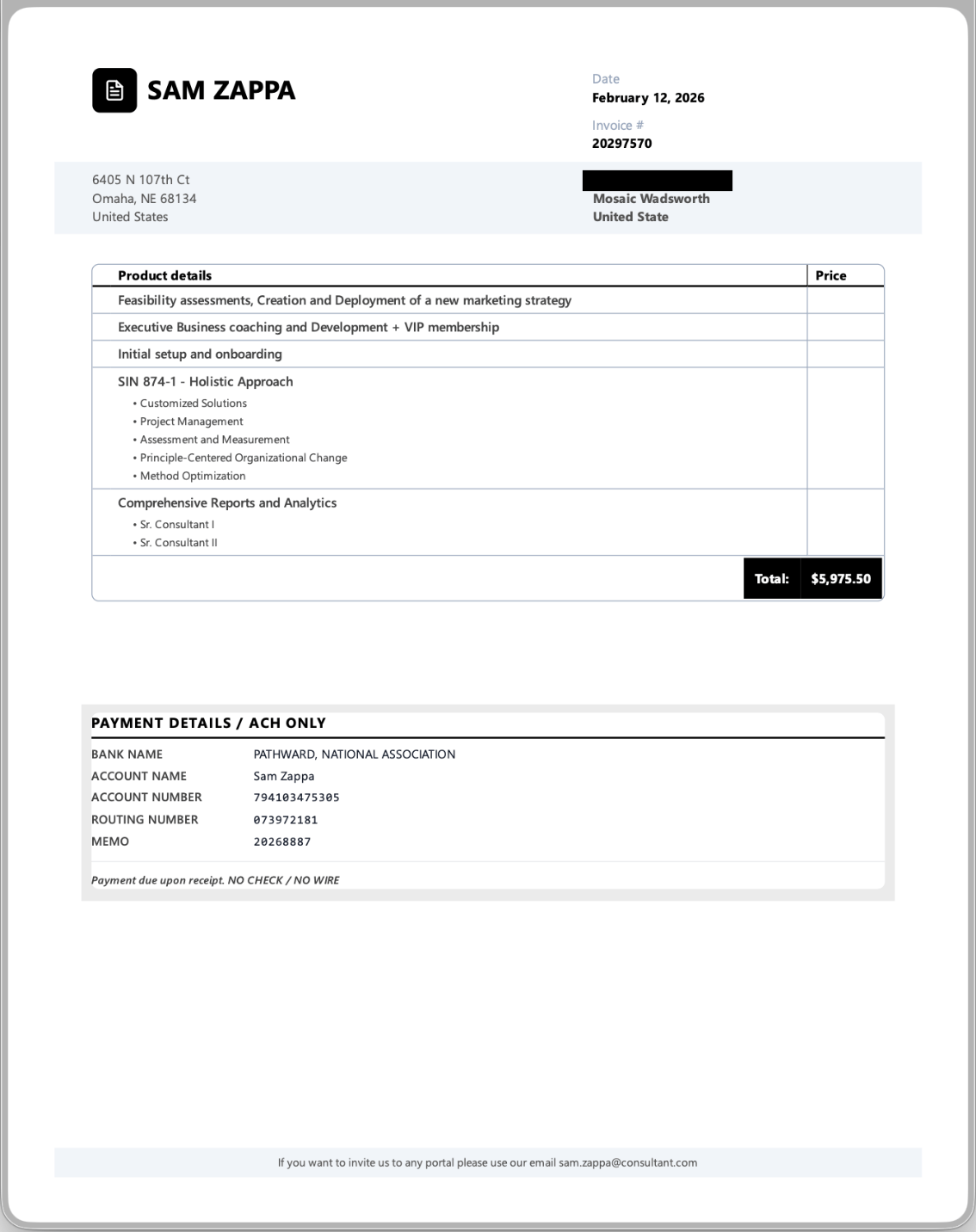
Combined ask: $10,951.00.
Both invoices directed payment via ACH only ("NO CHECK / NO WIRE") to a Pathward National Association bank account. Pathward, formerly MetaBank, is the bank behind most prepaid debit cards and fintech apps. It's the go-to for mule accounts in BEC fraud. ACH to a Pathward account is the hardest payment method to recover.
The Fabricated Thread
Below the cover email was a manufactured conversation chain, four layers deep, designed to make it look like the whole thing had already been vetted and approved by leadership.
Layer 1: A "welcome" email from Sam Zappa to Adam B*, dated January 12, welcoming him to the "Vistage Executive Advisory VIP Club." Vistage is a real executive coaching organization. The name-drop adds instant legitimacy.
Layer 2: A follow-up reminder two days later. "The outstanding balance of $5,975.50 USD remains unpaid."
Layer 3: A reply from "Adam B*" (our lead pastor) back to Sam Zappa. This is the load-bearing layer:
I did receive your invoice email. However, I was under the impression that a copy had already been forwarded to our Accounts department, as outlined during the initial setup. Could you kindly confirm whether this was done? If not, would you please send a copy directly to our Accounting Department at **********@mosaicwadsworth.com?
Read that from an AP processor's perspective. The lead pastor already knows about this. The lead pastor already approved it. He's asking why AP hasn't paid yet. That's an incredibly powerful social override.
Layer 4: The cover email, forwarding the whole chain to AP with a "please pay" wrapper.
The entire thread was fabricated. None of it happened. But it read like three months of legitimate correspondence.
The Tells They Almost Hid
This attack was good. Really good. But every scam has seams.
"Hi Tevin." In the fabricated Adam B* reply, the greeting says "Hi Tevin," but the sender's name is Sam. This is a template reuse error. The attacker ran this playbook against other organizations, and a name from a previous campaign leaked into the Mosaic version.
Empty email addresses. Every "Adam B*" message in the fabricated thread had empty angle brackets in the From field: Adam B***** <>. No actual email address. A real forwarded chain would show the sender's address.
Cyrillic character substitution. The word "Executive" in the subject lines wasn't actually the word "Executive." Several letters were replaced with visually identical Cyrillic characters: Е instead of E, χ instead of x, і instead of i, ν instead of v. The word renders normally to human eyes but bypasses keyword-based spam filters that scan for English text. This is a known obfuscation technique, and spotting it requires viewing the raw HTML source.
"United State." Both invoices listed the billing country as "United State," missing the 's'. A small typo, but it appeared on both PDFs, confirming they were generated from the same template.
The Outlook banner. Microsoft flagged it: "You don't often get email from [email protected]." That gray safety banner is easy to scroll past. Most people do.
Why This One Was Different
Most phishing emails fail because they don't match reality. This one did.
Adam had actually been talking to a consulting company at the beginning of the year. So an invoice for executive coaching and business development services tied to his name? Not crazy. Not out of the blue. It matched something that had actually been happening.
And the AP mailbox detail: the fabricated "Adam" reply asking for the invoice to be forwarded to our Accounts Payable email? We had only switched to using a shared AP address in the past two months. That process was still new. The email read like Adam was doing exactly what we'd asked everyone to do: route invoices through the new AP workflow.
Two coincidences. Both real. Both made this email feel like it belonged.
💡 The Social Engineering Trap
"Spam hopes you don't look. Social engineering hopes you look and see exactly what you expect to see."
The One Question That Caught It
The thing that kept this from becoming a disaster wasn't a spam filter. It wasn't a security tool. It wasn't even a red flag I spotted in the email itself.
It was a passing conversation on a Sunday morning.
I caught Adam in the hallway right before he went up to preach. Quick sidebar. Casual. "Hey, was the invoice for the consulting company you had forwarded to us legit? The first one was for roughly five grand."
He looked at me blank. No idea what I was talking about.
We went back and forth for a minute. After the service, he sat down with me and looked at it. He'd never heard of the company. He'd never had the conversation. The entire email thread, every layer of it, was completely fabricated.
One question. That's all it took.
But here's the part that keeps me up at night. I am currently onboarding a new AP assistant. He doesn't have the same level of pattern recognition I do when it comes to spotting scams. He's been out of town for the past two weeks, which is the only reason he didn't see this email first. If this had landed in the AP inbox on a normal week, and he had processed it the way the email was designed to make him process it, it could have gone through. Low probability: He knows to verify any unusual transaction over $1,000 before sending payment. Low, but not zero. He has the ability to push the button to send that much money out of our account. If he had heard Adam talking about the possible consultant at the beginning of the year, he may not have given it a single thought.
The attack wasn't designed to fool me. It was designed to fool the person who processes invoices. And it was timed, whether by luck or by design, to arrive during a window when the normal scrutiny might not have been there.
What We Did
Once the email was flagged, took some steps.
Preserved everything. I pulled the full email content, headers, and metadata through the Microsoft 365 API. Documented the complete fabricated thread across all four layers. Screenshot and transcribed every detail from the three PDF attachments: the W-9 data, both invoice line items, the bank account and routing numbers, the payment instructions.
Listed the red flags. Unicode obfuscation, empty From fields, template name errors, typo patterns, domain analysis on all three email addresses involved. Every indicator that this was manufactured went into a preservation document.
Filed an IC3 complaint. The FBI's Internet Crime Complaint Center is the federal clearinghouse for business email compromise. We filed the full report: the Pathward bank account number, the routing number, the SSN from the fraudulent W-9, all three attacker email addresses, the physical address from the invoices. Even though no money was lost, those financial details are how the FBI connects cases. The same bank account hitting 50 churches is a pattern. Our report becomes one data point in that pattern.
Reported to Microsoft. The original email in the AP mailbox was reported through Outlook's phishing report flow. That feeds Microsoft's spam filter training. The next variant of this template has a slightly better chance of getting caught before it reaches an inbox.
What This Means for Your Church
If your church has a shared AP or accounts payable mailbox, it is a target. Not theoretically. Not eventually. Right now.
This attack wasn't a Nigerian prince email. It wasn't a misspelled PayPal phishing link. It was a professionally packaged vendor onboarding, complete with W-9, sequential invoices, GSA references, and a fabricated approval chain using your actual lead pastor's name. The person processing invoices in your finance office would have no reason to question it unless they had a specific policy that forced them to.
The W-9 trick changes the game. "We already have their paperwork on file" used to be a reasonable signal that a vendor was legitimate. It's not anymore. If an attacker can generate a convincing W-9, the paperwork checkpoint becomes theater.
The one defense that still works: Any invoice over a threshold amount from a new vendor requires a verbal confirmation. A phone call to the pastor or executive whose name is on the approval, using a number you looked up yourself. Not a number from the email. Not a reply to the thread. A call to a number you already had.
🛑 The Golden Rule of AP
"Any invoice over a threshold amount from a new vendor requires a verbal confirmation. Use a phone number you already have on file—never a number provided in the email thread or the invoice itself."
File IC3 reports even when no money is lost. The bank account, routing number, and SSN on that W-9 are the most traceable artifacts in the entire attack. They may already be linked to dozens of other complaints. Your report adds weight to a case that's being built whether you participate or not. It takes 15 minutes. Do it at ic3.gov.
The mission matters too much to let the infrastructure, even the financial infrastructure, go undefended.
